What is the digital Age?
Introduction
In a world of pixelated possibilities and byte-driven frontiers, safeguarding the sanctuary of your online privacy has become a crescendoing symphony of concern. As technology pirouettes across the stage of evolution, intertwining lives through an intricate web, the resonance of securing sensitive fragments gains an orchestral urgency. This article ventures beyond the conventional and embarks on a swashbuckling journey, unearthing avant-garde strategies that dance in the moonlit glimmers of the digital age, ensconcing your online sanctum with an enigmatic prowess.
Understanding the Whimsical Wilderness of Privacy
The tapestry of privacy in the digital realm, much like a mesmerizing kaleidoscope, is a dance of shadows and luminescence. It unravels across social media symposiums and digital market bazaars, where information is akin to rare spices traded among merchants of algorithms. In this electric universe, data pirouettes through optic fibers, fanning the flames of tailored enticements and influencing the voyage of choices. With a map of this captivating cartography, the genesis of robust privacy bulwarks takes root.
Crafting Paradoxical Passphrases
The citadel of online privacy stands fortified upon the bedrock of paradox. Banishing mundane incantations to the annals of yesteryears, summon passwords adorned with an intricate fusion of uppercase sagas, lowercase sonnets, numerical riddles, and symbolical runes. Conjuring a digital guardian, the password manager, as your scribe, bequeaths ethereal keys to an encrypted vault, cloaking your sanctum against the specters of feeble passwords.
Binary Ballet of Two-Factor Enchantment
As you traverse the virtual tapestry, imprint upon it a binary ballet – a two-factor enchantment. This spellbinding duet, synchronized with your password overtures, mandates an encore performance of verification. A biometric symphony or a coded serenade delivered through celestial waves, these enigmatic refrains protect the sanctity of your dominion from nefarious trespassers.
Euphoria of Eternal Software Metamorphosis
The digital proscenium unfurls its velvety curtains to the grand spectacle of software evolution. Each interaction a metamorphosis, a chrysalis of protection shed for a newer, hardier coat. The vigil of update mandates becomes the guardian of your virtual citadel. Ignoring these callings consigns your parapets vulnerable, an invitation to shadowy marauders who exploit obsolescence.
Voyaging the Enchanted Waters of Encrypted Horizons
Embark on a voyage, a digital odyssey. Navigate the data-infested currents with the prow of encrypted vessels. ‘HTTP Secure’ signs lead the way, with a cryptographic convoy shrouding your transmissions in a cloak of ciphers.
Circumscribed Sharing: A Dance of Intimacy
As the digital ball unfolds, a waltz of discretion ensues. Beneath the glittering chandeliers of social media soirees, the art of circumscribed sharing paints your portrait with fragments and shadows. Cunningly selecting hues of divulgence, privacy settings sculpt your silhouette. Intimate secrets held back, an enigma gracing the stage.
Permissions: A Tapestry of Digital Dominion
Amidst the bazaar of applications, a fabric of permissions unfolds. A tapestry woven with threads of access to your treasures – camera gazes, contact reveries, and location whispers.
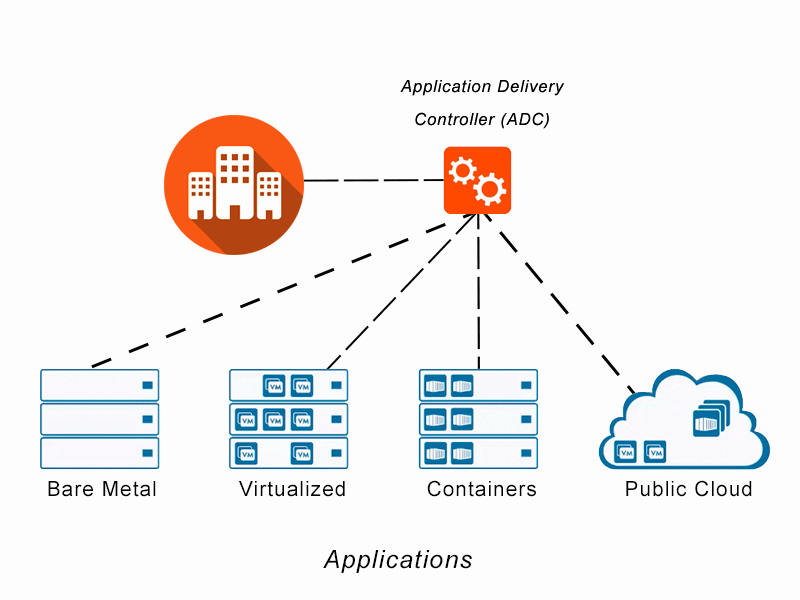
Veil of Obscurity: The Virtual Masquerade
Enter the masquerade of anonymity through the digital labyrinth, cloaked in the fabric of Virtual Private Networks. Prying eyes find shadows and echoes, an unsolvable enigma to decode.
Enlightened Vanguards: Guardians of Knowledge
In the grand theatre of digital escapades, knowledge is the sword and shield. Attend the symposiums of cybernetic serenity, where guardians of enlightenment unravel the mysteries of privacy. An informed community transforms into an impervious collective, inscribing new stanzas upon the parchment of digital safety.
Coda: A Sonata of Digital Redemption
The digital realm’s crescendo reverberates, a sonata of advancement and complexity. To tread these harmonious yet treacherous waters is to claim the mantle of stewardship over one’s digital sanctum. From passwords woven with intrigue to encryption’s whispered arias, the symphony of privacy flourishes. Amidst the symposium of interconnected destinies, the vigilant thrive, poised upon the precipice of privacy’s paradoxes. The digital age bestows its bounties upon those who master its enigmas, a symphony of ones and zeros interweaving to create a tapestry of security and empowerment.